华为模拟器NAT地址转换技术
发布时间:2021-05-06
NAT产生背景
- IPv4地址日渐枯竭
- IPv6技术不能立即大面积替换
各种延长IPv4寿命的技术不断出现,NAT就是其中之一.
为什么需要NAT?
- NAT技术主要应用是实现大量的私网地址对少量公网地址的转换,保障通信在基础上节约IP地址资源.
私网地址不能在公网中路由,否则将导致通信混乱.
NAT技术的基本原理
NAT技术通过对IP报文头中的源地址或目的地址进行转换,可以使大量的私网IP地址通过共享少量的公网IP地址来访问公网.
NAT分类
源NAT
- 地址池方式
- 出接口地址方式(Easy IP)
服务器映射
- 静态映射(NAT server)
目的NAT
NAT的优点与缺点
优点
- 实现IP地址复用,节约宝贵的地址资源
- 地址转换过程对用户透明
- 对内网用户提供隐私保护
- 可实现对内部服务器的负载均衡
缺点
- 网络监控难度加大
限制某些具体应用
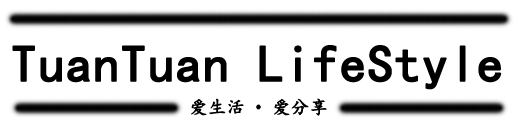
NAT 地址池
NAT地址池是一些连续的IP地址集合,当来自私网的报文通过地址转换到公网IP时,将会选择地址池中的某个地址作为转换后的地址
创建NAT地址池的命令为:nat address-group address-group-name
section [ section-id | section-name ] start-address end-address
nat-mode { pat | no-pat }
例:
[USG] nat address-group testgroup1
[USG-nat-address-group-testgroup1] section 1.1.1.10 1.1.1.15
[USG-nat-address-group-testgroup1] mode pat(pat表示地址转换的同时进行端口的转换,no-pat表示地址转换的同时不进行端口的转换)
配置源NAT策略 (CLI)
首先配置NAT地址池(省略)
在系统视图下进入NAT策略视图
nat-policy 在NAT策略视图下创建NAT规则并进入NAT规则视图
rule name rule-name创建NAT策略,进入策略ID视图
source/destination-address { address-set address-set-name &<1-6> | ipv4-address
source/destination-zone { zone-name &<1-6> | any }
egress-interface interface-type interface-number
service { service-name &<1-6> | any }
action {source-nat { { address-group address-group name } | easy-ip } 基于NAT Server的配置 (CLI)
在系统视图下:
nat server [ id ] protocol protocol-type global { global-address [ global-address-end ] | interface interface-type interface-number } inside host-address [ host-address-end ] [ no-reverse ][ vpn-instance vpn-instance-name2 ]例:
nat server server1 protocol tcp global 202.202.1.1 inside 192.168.1.1基于目的NAT的配置(CLI)
在系统视图下,进入安全区域视图,配置目的NAT
firewall zone [ name ] zone-name
destination-nat acl-number address ip-address [ port port-number ]举例:
[USG] firewall zone trust
[USG-zone-trust] destination-nat 3333 address 202.1.1.2双向NAT技术
双向NAT两种应用场景:
- NAT Server + 源NAT
域内NAT
防火墙源NAT配置(CLI)
配置域间访问规则。
指定源地址为192.168.0.0网段(具体配置步骤省略)
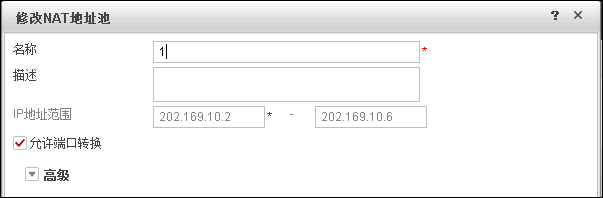
配置地址池
[USG6600] nat address-group 1
[USG6600-nat-address-group-1] section 202.169.10.2 202.169.10.6
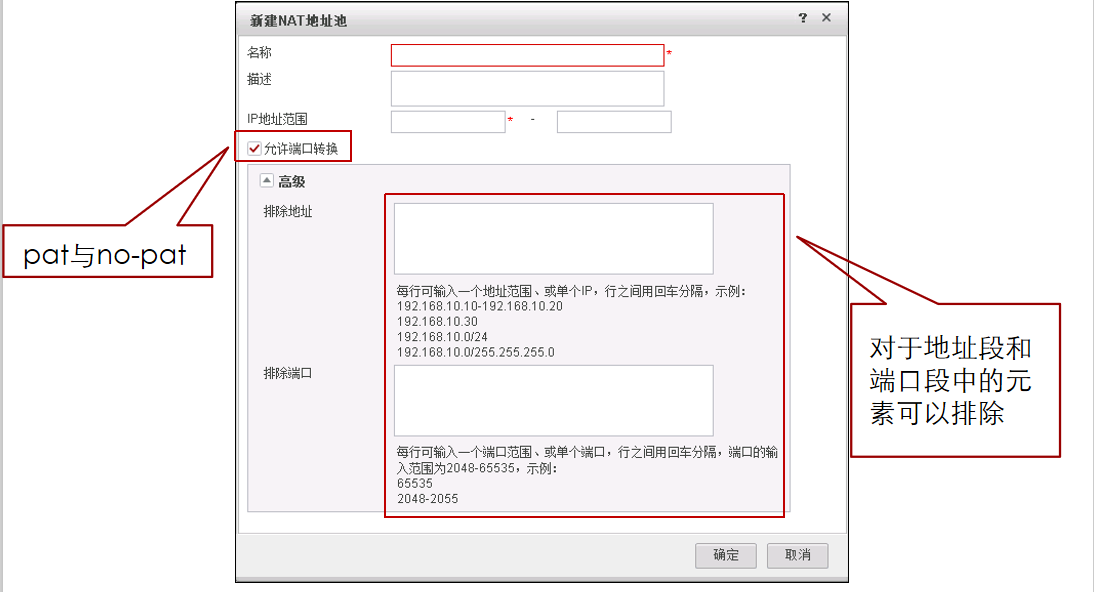
配置源NAT策略
[USG6600] nat-policy
[USG6600-policy-nat] rule name nat1
[USG6600-policy-nat-rule-nat1] source-zone trust
[USG6600-policy-nat-rule-nat1] destination-zone untrust
[USG6600-policy-nat-rule-nat1] source-address 192.168.0.0 24
[USG6600-policy-nat-rule-nat1] action nat address-group 1防火墙源NAT配置(WEB)
配置源NAT策略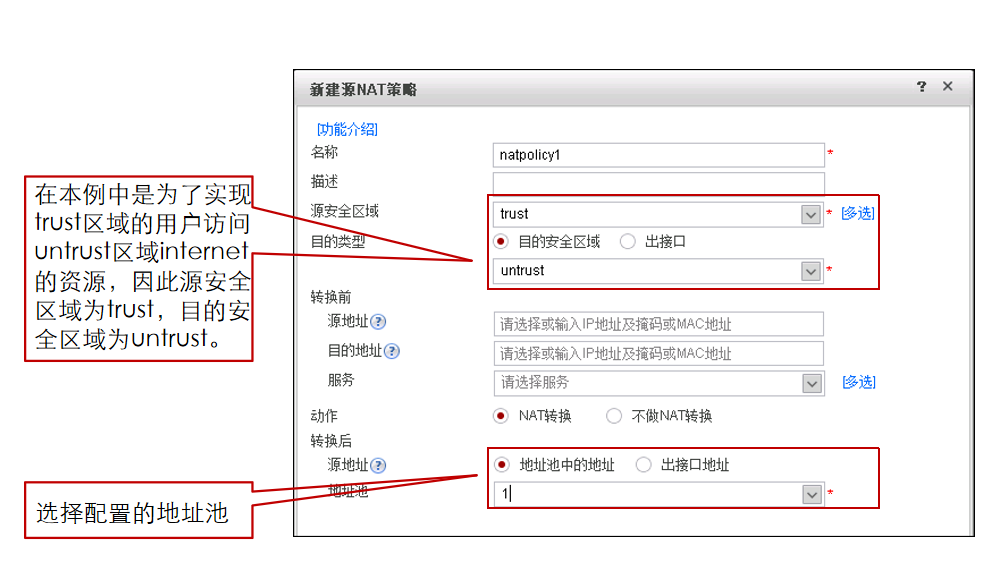
防火墙NAT Server配置 (CLI)
配置内部Web和FTP服务器
[USG] nat server wwwserver protocol tcp global 202.169.10.1 80 inside 192.168.20.2 8080
[USG] nat server ftpserver protocol tcp global 202.169.10.1 ftp inside 192.168.20.3 ftp
配置域间包过滤规则[USG] security-policy
[USG -policy-security] rule name p1
[USG -policy-security-rule-p1] source-zone untrust
[USG -policy-security-rule-p1] destination-zone dmz
[USG -policy-security-rule-p1] destination-address 192.168.20.2 32
[USG -policy-security-rule-p1] service http
[USG -policy-security-rule-p1] action permit
[USG -policy-security] rule name p2
[USG -policy-security-rule-p2] source-zone untrust
配置内部Web和FTP服务器(web)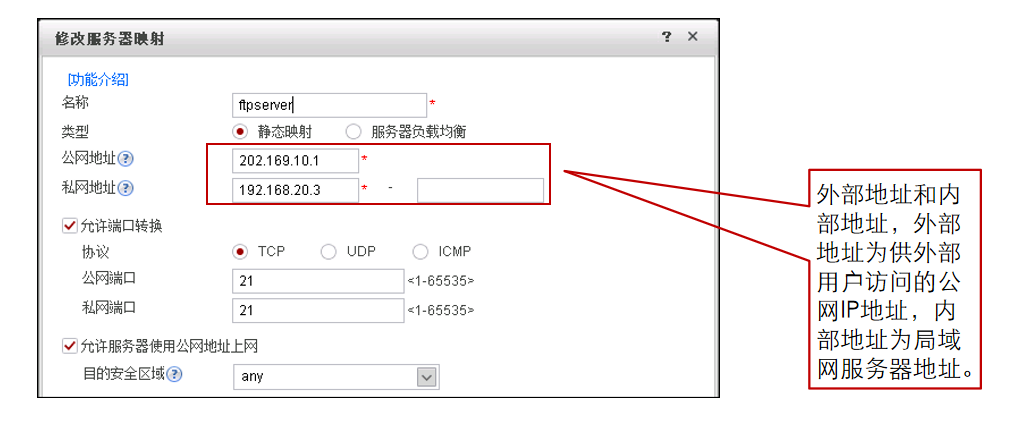
配置域间安全转发策略[USG -policy-security-rule-p2] destination-zone dmz
[USG -policy-security-rule-p2] destination-address 192.168.20.3 32
[USG -policy-security-rule-p2] service ftp
[USG -policy-security-rule-p2] action permit
配置域间安全转发策略(web)
NAT双出口配置 - 1 (CLI)
创建安全区域 为ISP1和ISP2分别创建一个安全区域
[USG] firewall zone name ISP1
[USG-zone-isp1] set priority 10
[USG] firewall zone name ISP2
[USG-zone-isp2] set priority 20
配置各接口的IP地址,并将其加入相应的安全区域(配置省略)
配置域间安全转发策略。开启内网到ISP1和ISP2区域的outbound方向策略
[USG] security-policy
[USG-policy-security] rule name NAT_dual_egress
[USG-policy-security-rule-NAT_dual_egress] source-zone trust
[USG-policy-security-rule-NAT_dual_egress] destination-zone isp1 isp2
[USG-policy-security-rule-NAT_dual_egress] source-address 10.1.1.0 24
[USG-policy-security-rule-NAT_dual_egress] action permit
配置静态路由保证路由可达
假设通过ISP1和ISP2访问internet资源的下一跳地址分别为1.1.1.2/24和2.2.2.2/24(具体步骤省略)
配置源NAT策略
[USG] nat-policy
[USG-policy-nat] rule name NAT_dual_egress
[USG-policy-nat-rule-nat_dual_ergess] source-zone trust
[USG-policy-nat-rule-nat_dual_ergess] destination-zone isp1 isp2
[USG-policy-nat-rule-nat_dual_ergess] egress-interface GigabitEthernet 1/0/4
[USG-policy-nat-rule-nat_dual_ergess] egress-interface GigabitEthernet 1/0/5
[USG-policy-nat-rule-nat_dual_ergess] action source-nat easy-ip
配置域间安全转发策略。开启ISP1和ISP2区域到内网方向策略。(ISP2的配置与ISP1相似,具体配置省略)
[USG] security-policy
[USG-policy-security] rule name nat_server
[USG-policy-security-rule-nat_server] source-zone isp1 isp2
[USG-policy-security-rule-nat_server] destination-zone trust
[USG-policy-security-rule-nat_server] destination-address 10.1.1.2 32
[USG-policy-security-rule-nat_server] service ftp
[USG-policy-security-rule-nat_server] service icmp
[USG-policy-security-rule-nat_server] action permit
创建内网服务器的公网IP与私网IP的映射关系[USG] nat server zone isp1 protocol tcp global 1.1.1.1 ftp inside 10.1.1.2 ftp
[USG] nat server zone isp2 protocol tcp global 2.2.2.1 ftp inside 10.1.1.2 ftp
NAT ALG默认已经在防火墙全局开启,同时也可以单独在域间进行配置,使服务器可以正常对外提供FTP服务。#ftp默认开启,可以不做。
[USG] firewall interzone dmz isp1
[USG-interzone-dmz-isp1] detect ftp
[USG] quit
[USG] firewall interzone dmz isp2
[USG-interzone-dmz-isp2] detect ftp
[USG-interzone-dmz-isp2] quit
创建地址池:
[USG] nat address-group 2
[USG-nat-address-group-2] section 192.168.1.10 192.168.1.20 #将2.2.2.10转换成内部的地址访问192.168.3.2 默认mode=pat
创建NAT策略
[USG] nat-policy
[USG-policy-nat] rule name isp1
[USG-policy-nat-rule-biderectinal_nat] source-zone isp1
[USG-policy-nat-rule-biderectinal_nat] destination-zone dmz
[USG-policy-nat-rule-biderectinal_nat] source-address 1.1.1.0 24
[USG-policy-nat-rule-biderectinal_nat] action source-nat address-group 2
创建NAT策略
[USG] nat-policy
[USG-policy-nat] rule name isp2
[USG-policy-nat-rule-biderectinal_nat] source-zone isp2
[USG-policy-nat-rule-biderectinal_nat] destination-zone dmz
[USG-policy-nat-rule-biderectinal_nat] source-address 2.2.2.0 24
[USG-policy-nat-rule-biderectinal_nat] action source-nat address-group 2NAT双出口配置 - 1 (WEB)
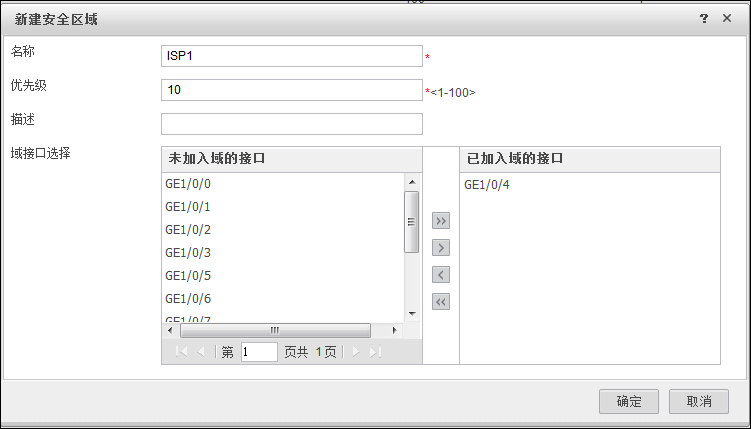
创建安全区域
配置域间策略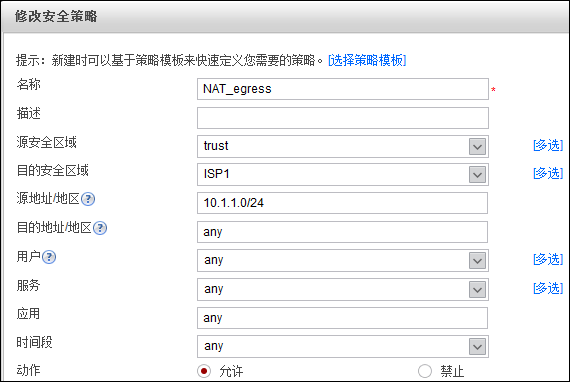
配置静态路由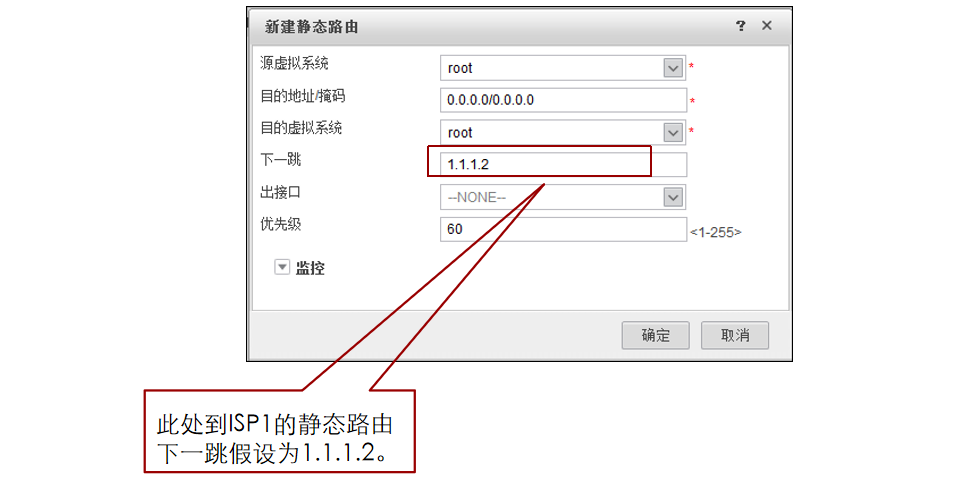
配置源NAT策略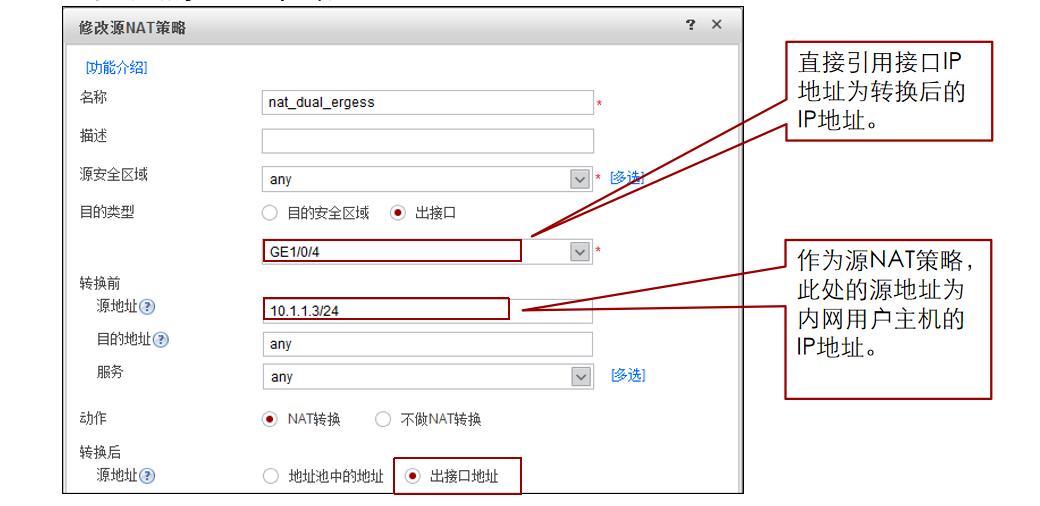
创建两台内网服务器的公网IP与私网IP的映射关系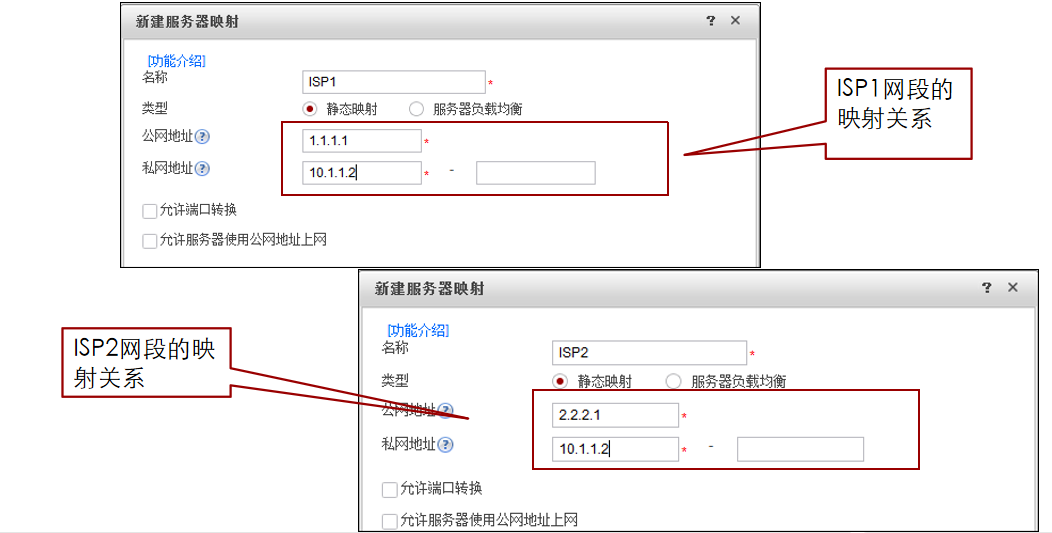
哇 你要支持我吗?太慷慨了!谢谢